The beginning of December saw around 3,200 security researchers, hackers, and developers gather in the east side of London to listen to over a hundred of their peers and learn the latest news and methodologies about information security.
The message to us as web developers was overwhelmingly that in order to create secure sites, you need to understand the techniques black hat hackers use. This means choosing a stack that has as few vulnerabilities as possible. The question was how good are you at making these vulnerabilities harder to exploit. In addition to that, most of the stuff we use as daily consumers is also extremely vulnerable, and I will never trust a printer again!

Simon and I travelled to London on behalf of Thorgate to see what Black Hat had to offer as one of the biggest cybersecurity conference in the world. Here’s our key takeaways:
Smart devices mean more attacks
An attack surface that gets bigger every day is IoT - there are already more than 17 billion devices worldwide that are constantly connected to the internet and the number increases every day. While these devices make our daily lives more convenient, this comes at a price called security.
The number of IoT malware has more than tripled since 2017 in just the first half of 2018, and 7.2 billion malware attacks were made in just the first three quarters of 2019. This means any company that either produces or uses IoT devices must think twice about every move they make, something that the security engineers Hikohiro Y Lin and Yuki Osawa from Panasonic made very clear to their audience at Black Hat.
This explains why security-minded people keep a good distance from any new smart and shiny tech and instead opt to use solid old-fashioned solutions.
New tech doesn’t mean good tech
Our service providers try very hard to make the technology we use daily faster and better. One such initiative is the RCS (Rich Communication Services) protocol aimed at upgrading the way SMS (Short Message Service) works. This technology has already been rolled out by over a 100 mobile operators. However, researchers at Security Research Labs have already found several ways in which a malicious attacker can track, impersonate, and defraud people using this protocol.
Techniques are forever, tools are not
Even though many of the talks demonstrated a specific way in which one could break into a specific device/program using specific tools, the keynote speaker Amanda Rousseau emphasized that the specifics are not important.
There will always be new tools available, and new devices or new programs. However, if you have an understanding of how they work, and why they work like they do, you will be able to stay a step ahead of your competitors. This is how to build the best applications, or be the best penetration tester, or even hack everything.
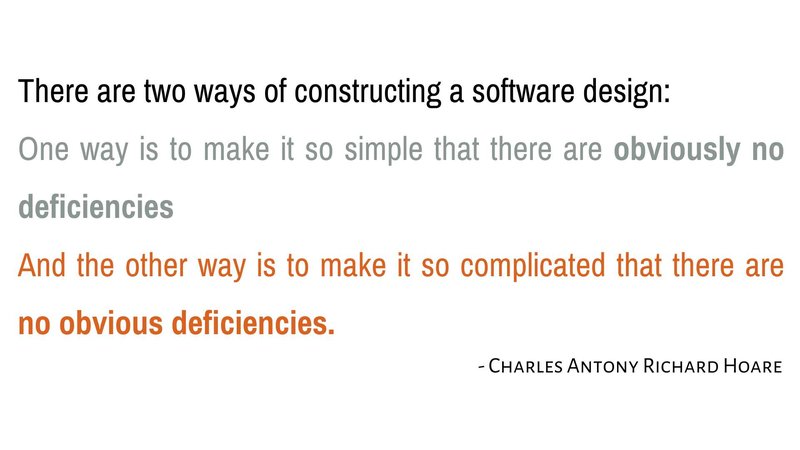
To conclude, here's my favorite quote pointed out by a presenter at Black Hat.